Configure Two-Factor Authentication (2FA)
To secure your account in the event that the account password has been compromised, two-factor authentication (2FA) is mandatory.
Software Vulnerability Research allows the following 2FA configuration options:
| • | Token-Based Two-Factor Authentication |
| • | SMS-Based Two-Factor Authentication |
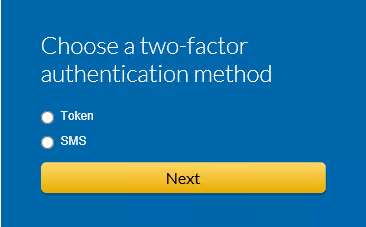
Choosing a Two-Factor Authentication Method
Token-based two-factor authentication is the default and recommended option.
In case your phone is lost or compromised, two-factor authentication can be reset. The reset method varies by account type. For details, see Two-Factor Authentication Recovery.